Prerequisites
Access Requirements
- Server Access:
- Confirm access to deployment servers with sudo privileges.
- Verify that all necessary network routes are established via a secure VPN or dedicated network configuration.
- User Permissions:
- Ensure that the deployment team has been granted the necessary access rights.
- Validate that any required two-factor authentication (2FA) or security tokens are in place.
System Requirements
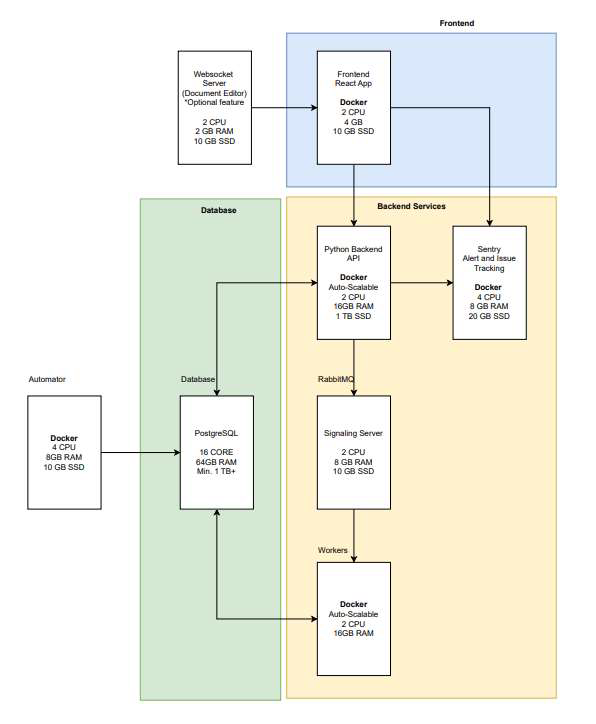
Operating System:Ubuntu 22 or RHEL 8.10 Hardware Specifications:
For each deployment tier, ensure that the hardware meets or exceeds the following:
| Tier | Cores | RAM (GB) | SSD |
|---|---|---|---|
| SMALL | 16 | 64 | 1TB |
| MEDIUM | 32 | 128 | 2TB |
| LARGE | Custom | Custom | Custom |
- GPU (Required when deploying an LLM on the same machine as the EKB platform.)
- SMALL: ~500 (100 Concurrent) users can be supported by a single VM 16 cores, 64gb ram, 1 TB
- SSD these machines cost ~$600 per month. This is a minimum size deployment.
- MEDIUM ~ 2000 (500 Concurrent) users can be supported by a larger machine 32 cores, 128gb ram, 2 TB
- SSD these machines are around ~$1,200 per month
- LARGE: ~10000 (1000+ Concurrent) users should be deployed across containers so that the infrastructure
- can scale to support the needs, this typically costs a minimum of $2,000 per month it is
- suggested to calculate $2,000 per month per additional 1,000 Active Users. This is a fully
Deployment Tools & Software Dependencies
- Deployment Scripts:
- Verified and version-controlled Bash deployment scripts.
- Dependency Management Tools:
- Python 3
- Git (current version)
- Docker (v27.1.1) or Podman
- Additional Tools (Optional):
- Logging and monitoring tools (e.g., ELK Stack, Prometheus, Grafana) as per the client’s monitoring requirements.
Credentials and Keys
- Server Credentials:
- Ensure that all server access credentials are up to date and securely stored.
- Application API Keys and Licenses:
- Verify that all application-specific API keys and licenses (e.g., OpenAI, SERP, Sentry) are available and valid.
Pre-Deployment Checklist
Hardware and System Verification
Ensure that the client’s hardware and system configurations match the specifications:3.2 Software and Dependency Verification
Verify that all necessary software components are installed and correctly versioned:3.3 Network and Connectivity Check
Ensure the network is correctly configured and that there is adequate internet connectivity for external dependencies or updates:3.4 Additional Verifications
Services and ports| Service | Path | Parameter | Internal ports | External ports |
|---|---|---|---|---|
| Frontend | / | FRONTEND_SUFFIX | 3000 | — |
| Nginx | / | — | — | 80, 443 |
| Backend | /backend | BACKEND_SUFFIX | 8001 | — |
| Automator | /automator | AUTOMATOR_SUFFIX | 8002 | — |
| Redis | — | — | 6379 | — |
| RabbitMQ | — | — | 5672, 15672 | — |
| Supabase Kong API Gateway | /supabase | SUPABASE_SUFFIX | 8000, 8443 | 8000, 8443 (admin only) |
| Supabase Postgres | — | — | 6543 | — |
| PostgreSQL (automator) | — | — | 5433 | — |
| Redis (automator) | — | — | 6380 | — |
| Ollama | — | — | 11434 | — (only if deploying Ollama locally) |
| Service | HTTP | HTTPS | WebSocket |
|---|---|---|---|
| Frontend | ✓ | ✓ | — |
| Nginx | ✓ | ✓ | — |
| Backend | ✓ | ✓ | — |
| Automator | ✓ | ✓ | — |
| Redis | ✓ | ✓ | — |
| RabbitMQ | ✓ | ✓ | — |
| Supabase Kong API Gateway | ✓ | ✓ | ✓ |
| Supabase Postgres | ✓ | ✓ | — |
| PostgreSQL (automator) | ✓ | ✓ | — |
| Redis (automator) | ✓ | ✓ | — |
| Ollama | ✓ | ✓ | — |
Notes: All internal machines must be able to communicate freely with each other. We recommend using SSL (HTTPS) connections; HTTP is supported during PoCs.Firewall and Security Settings: Validate that firewall rules or security groups allow for required traffic.
General Architecture
Architecture Diagram – OnPrem
Deployment architecture flow for single virtual machine box with mentioned prerequisite resource allocation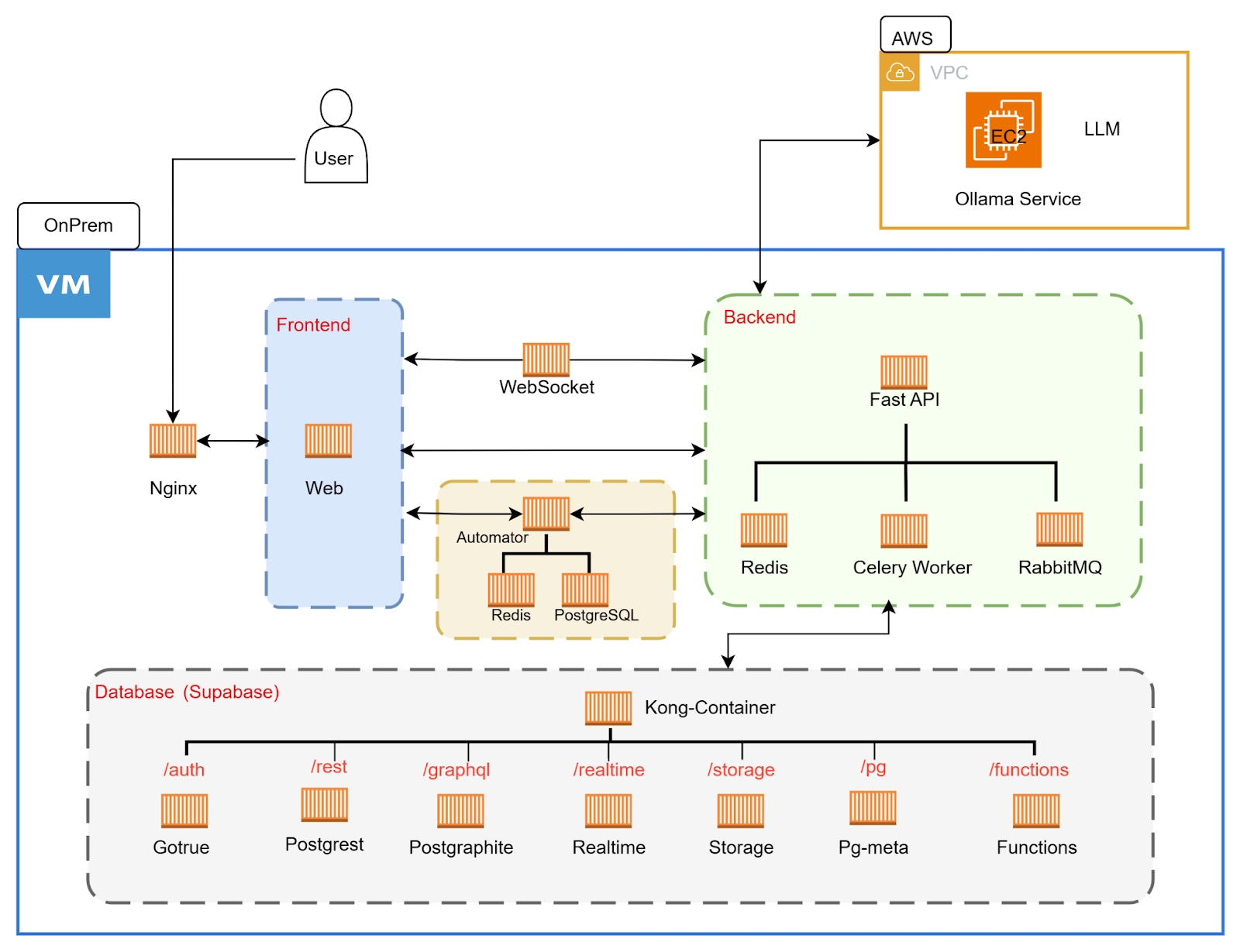
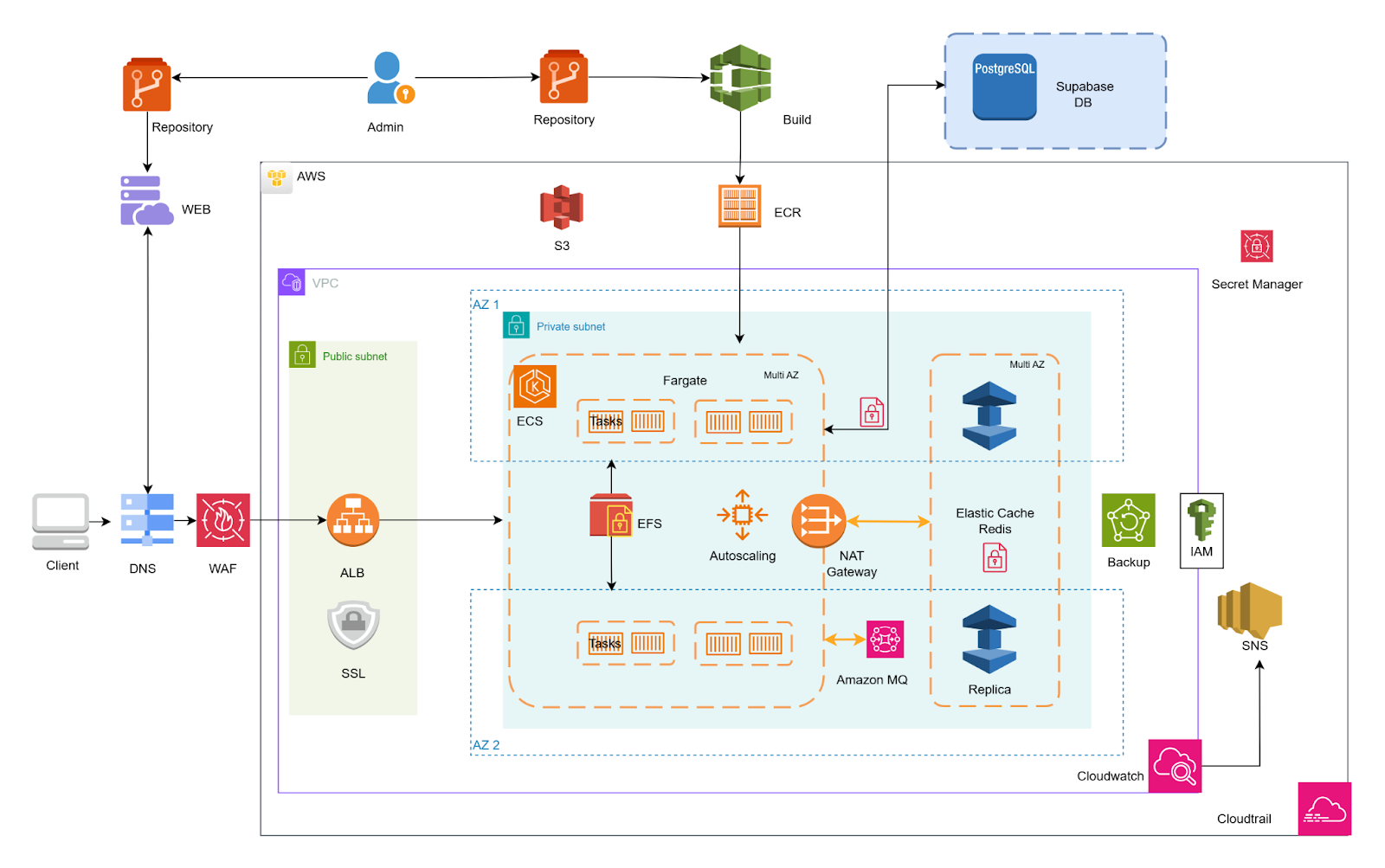
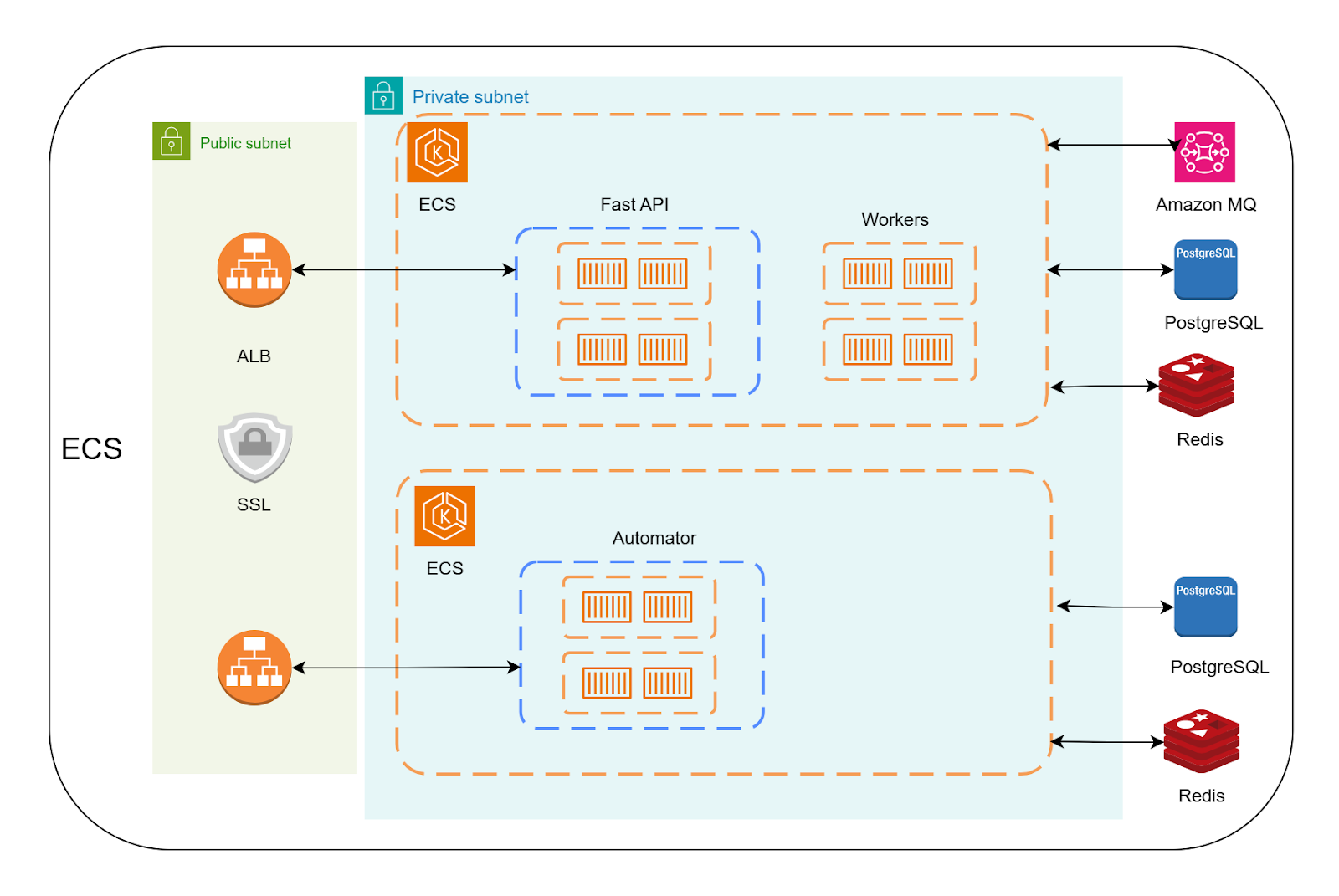
Deployment architecture flow for AWS Cloud deployment